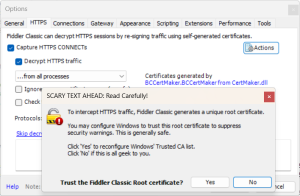
The following steps will guide you in creating a quick VPN connection using a certificate created in Windows via certmgr.msc. This can be necessary for multiple scenarios including:
- You have VMs that you would like to access which do not have public addresses assigned and are otherwise unreachable without a P2P connection.
- You want to test SMB Connections to Azure Files and port 445 is blocked by your ISP.
- Any number of other resources are not accessible publicly and you need a connection into the private vNET.
>> Take me straight to the steps! <<
Note: This type of VPN connection will allow you to connect to your resources in Azure, as opposed to connecting to the internet through new public IP addresses supplied by Azure to obfuscate or otherwise mask your internet location – if you are looking to create a VPN Gateway with which to access public internet locations with a new regional IP address; check out our other Post: >>> NNNN <<<<.
In our example, we have a private vNET and Subnet created in Azure with a VM on the subnet with no public IP Address. To encompass an additional scenario, we have also created a Storage Account with a File Share which has a Private Endpoint and public access set to disabled:
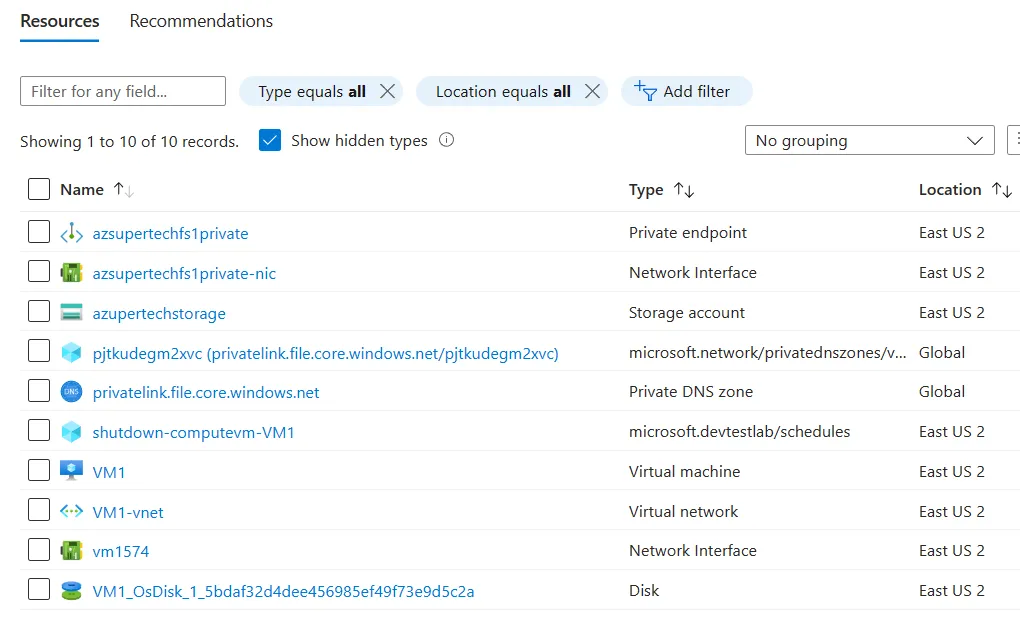
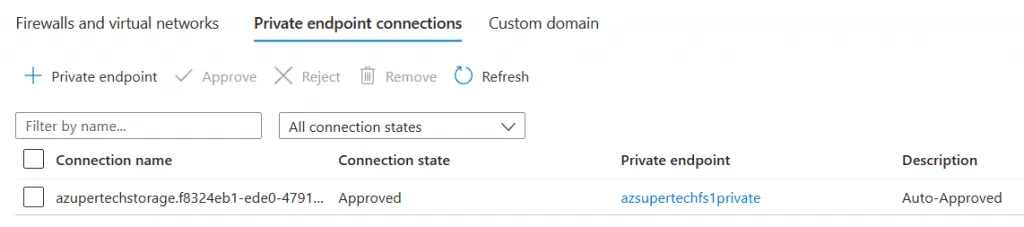
One issue you may encounter that may require you to create a VPN connection into an Azure private vNET may be that your Storage Account is only reachable via a Private Endpoint
- You would notice this due to the Networking option set: “Public network access Disabled”:
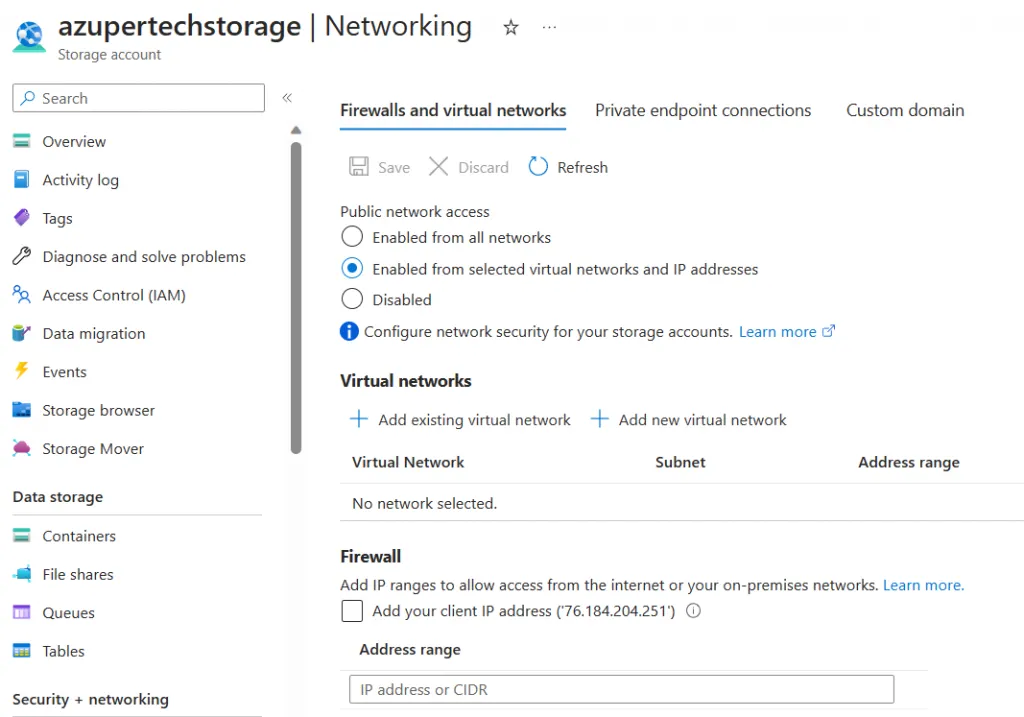
- Many users may not realize that when accessing a Storage Account through the Azure Portal from a Public connection, such rules remain preserved even in the portal view:
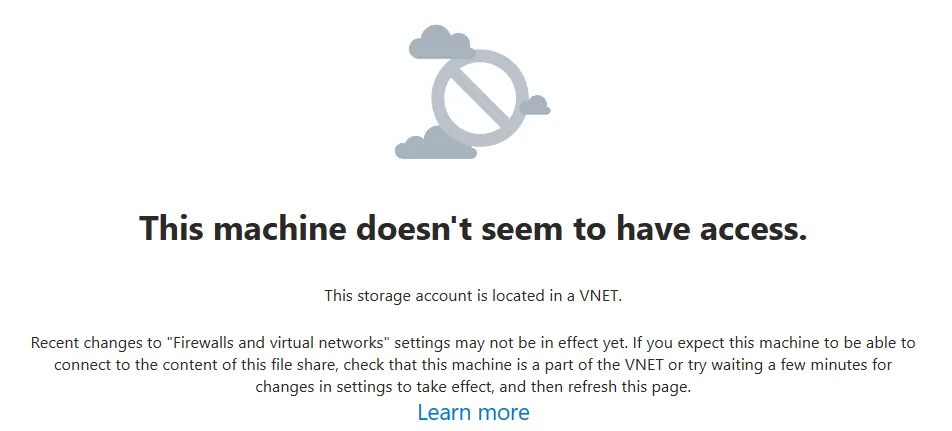
- For example, when attempting to browse to the File Share for the example Storage Account from the Portal we see the following error: “This machine doesn’t seem to have access” – “this storage account is located in a VNET”:
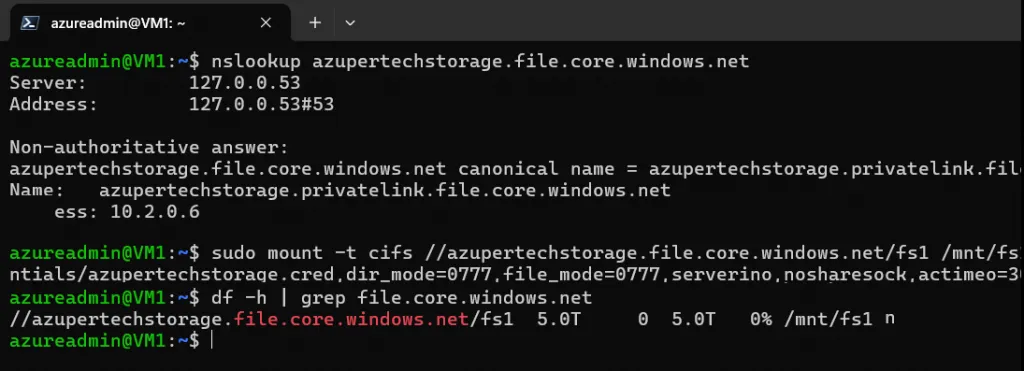
- In comparison, since this Storage Account has a Private Endpoint (as is required to access the storage account, per the Network/”Firewall” setting), we can see that the VM in the same subnet where the private link is located, has no issue accessing the file share:
Steps to create your VPN Gateway using certmgr.msc for certificates in Windows:
- From your Resource Group choose + Create, this will bring you to the Marketplace where you can search for: Virtual network gateway and create a Virtual network gateway resource:
- When creating the Virtual Network Gateway, be sure to choose the appropriate Virtual Network where your resources reside:
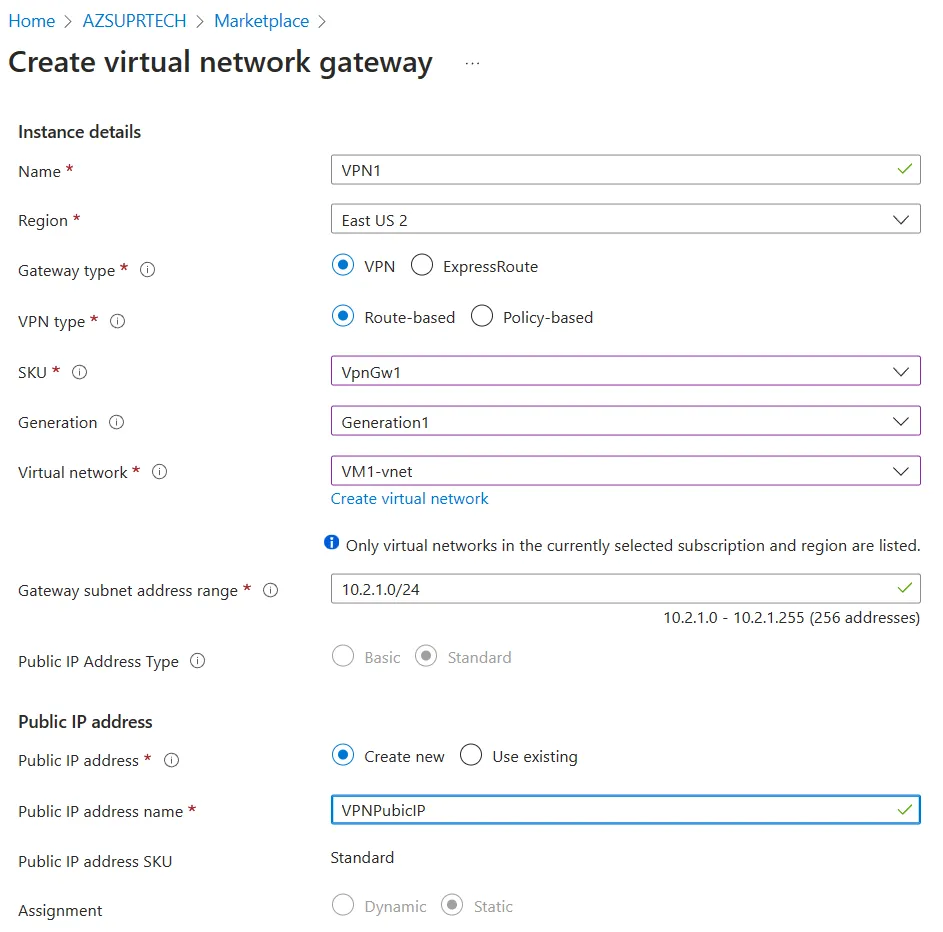
- Note that in the above example, we are creating a Gateway subnet in the existing address range of the vNET and a new Public IP address is created for the VPN.
- Once deploying the Virtual Network Gateway, the deployment will take considerable time (around 30 minutes).
While waiting for the Virtual Network Gateway to finish deploying, you can create your root certificate in PowerShell and export it using certmgr.msc:
- Open PowerShell and perform the following:
# Create a root certificate variable $rootcert
$rootcert = New-SelfSignedCertificate -Type Custom `
-Subject "CN=P2SROOT" `
-KeyExportPolicy Exportable `
-KeySpec Signature `
-HashAlgorithm sha256 `
-KeyLength 2048 `
-CertStoreLocation "Cert:\CurrentUser\My" `
-KeyUsageProperty Sign `
-KeyUsage CertSign# Create a new Self-Signed certificate
New-SelfSignedCertificate -Type Custom `
-DnsName P2SCLIENT `
-KeySpec Signature `
-Subject "CN=P2SCLIENT" `
-KeyExportPolicy Exportable `
-HashAlgorithm sha256 `
-KeyLength 2048 `
-CertStoreLocation "Cert:\CurrentUser\My" `
-Signer $rootcert `
-TextExtension @("2.5.29.37={text}1.3.6.1.5.5.7.3.2")
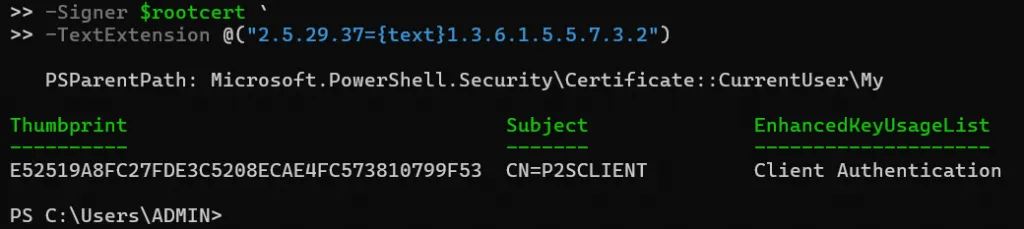
The above script will create a root certificate variable $rootcert and then create a new self signed certificate sourcing the -Signer $rootcert via New-SelfSignedCertficate
- Output for the New-SelfSignedCertificate command should yeild a Thumbprint and Certificate Name (Subject):
- After creating the certificate, we can view it via the local Certificate Manager:
- Right Click the Start Button in Windows and choose Run or Hit WIN+R:
- certmgr.msc <Enter>
- Browse to:
- Certificates – Current User > Personal > Certificates > PSROOT Certificate
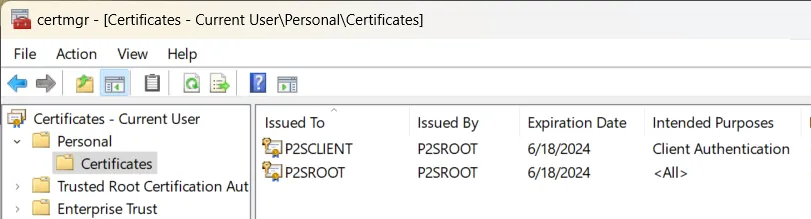
- Right Click the certificate labeled as “<All>” and choose: All Tasks > Export…
- Choose options: Next > No, do not export the private key > Next > Base-64 encoded X.509 (.CER)
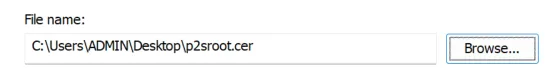
- Save the file as p2sroot.cer to your desktop by entering the filename, choosing Next and Finish
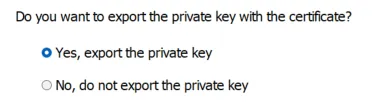
- Now, right click the alternate entry labled as “Client Authentication” and choose: All Tasks > Export:
- Choose: Next, Yes, export the private key, Next
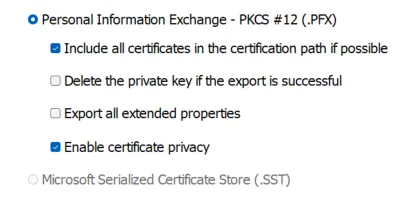
- Leave the default option for “Personal Information Exchange – PCKS #12 (.PCX)
- Leave boxes checked for “Include all certificates…” & “Enable certificate privacy” and choose Next
- In the next section you are required to set a password, type a memorable password twice (after checking the Password box) and choose Next.
- Enter the file name p2sroot.pfx and export the file your desktop (Next, Finish).
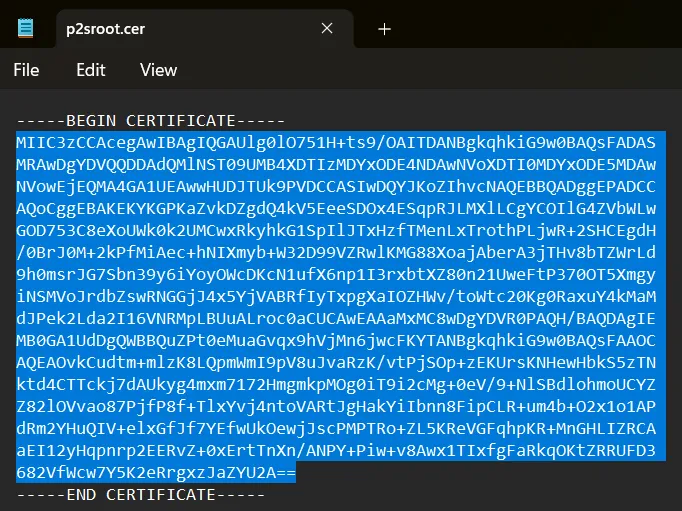
- Open the p2sroot.cer file in Notepad and copy the key as you will need it in the next step:
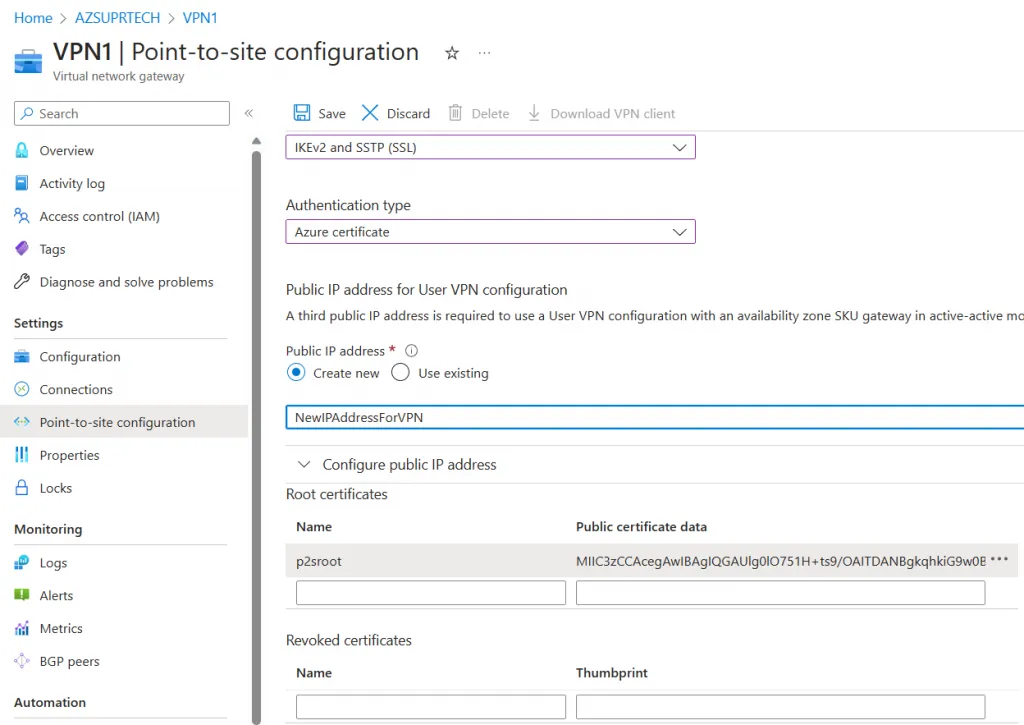
By now, if 30 minutes have passed; your Virtual Network Gateway deployment should be complete (note, this can sometimes this can take up to 45 minutes). Go to your Virtual Network Gateway resource and choose: Point-to-site configuration > Configure now:
- Pick an address pool which differs from your connected subnet, for example: If your subnet is 10.1.1.0/24 you may want to pick 172.10.10.0/24.
- For the Tunnel type choose: IKEv2 and SSTP (SSL)
- If prompted for Puplic IP address, create a new or appropriate IP
- Under Root certificates, name your p2sroot certificate and paste in the key vaulue from notepad:
- Once you have saved the Point-to-site configuration you will see another “Deployment in progress… ” notification
- Once the deployment has completed (note that this can also take around 30 minutes):
- Refresh the Point-to-site configuration page to reveal the Download VPN client button:
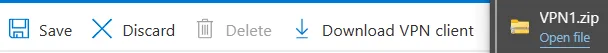
- Download the Client ZIP file, extract the WindowsAmd64 (or appropriate) folder and run the containing VpnClientSetupAmd64.exe installer.
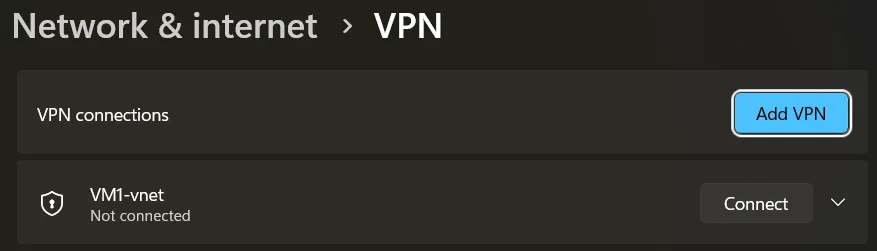
- After the installer has ran, choose the Network Icon in your taskbar to see the VPN Client and choose Connect:
- In Windows 11, this should take you to: Setting > Network & Internet > VPN
- Choose Connect:
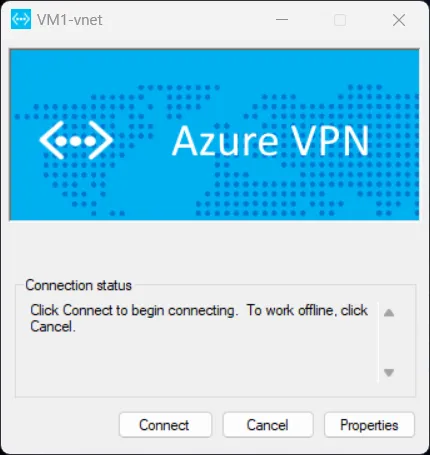
- After choosing Connect > “Do not show this message again” for the elevated priveledge/CMROUTE.DLL message > Continue > Yes, the VPN should be connected.
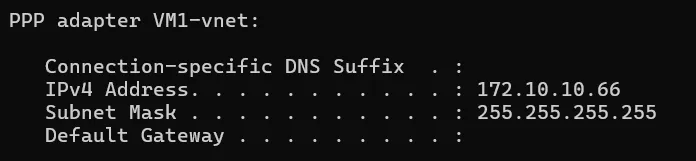
- Notice validation of the connection from Windows Terminal per IPCONFIG:
- You will also see the client connection under: Point-to-site Sessions under the Virtual network gateway:

What can we do now that we are connected to our newly created VPN Connection?
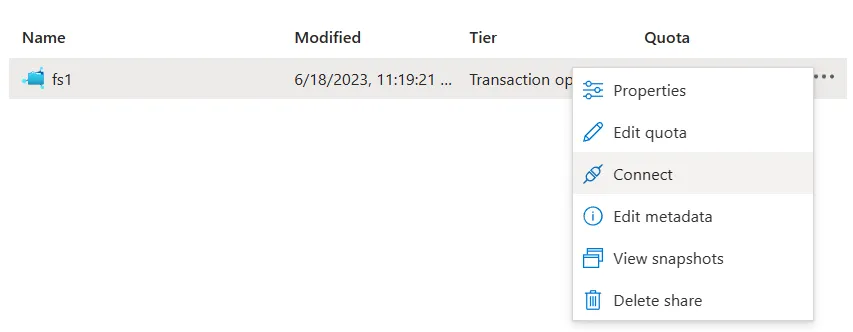
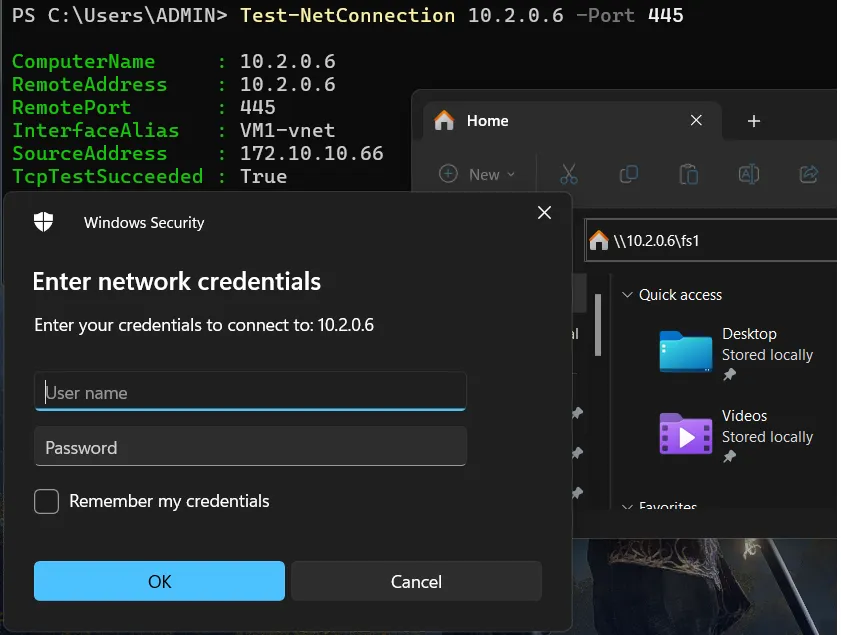
- We can now connect directly to our Azure File Share from our Windows Machine, outside of Azure over the VPN through the private endpoint:
- Normally, in order to resolve the Private Endpoint you would need to resolve DNS appropriatly, however we can cheat for our test and reference the private IP address of the storage account directly via: Storage Account > Networking > Private endpoint connections > Private Endpoint Name > Network interface:
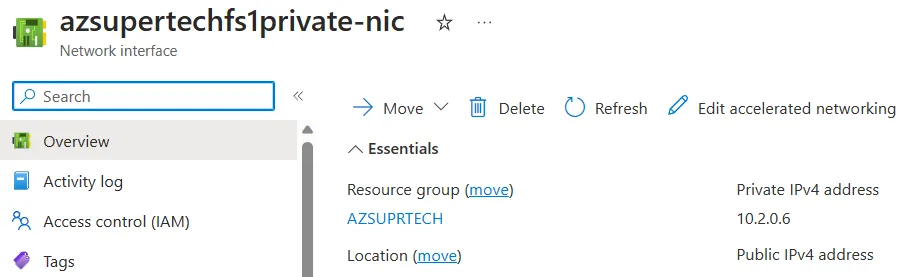
- We can now see that we can access the File Share over the private endpoint/IP/NIC without issue from the VPN Connection:
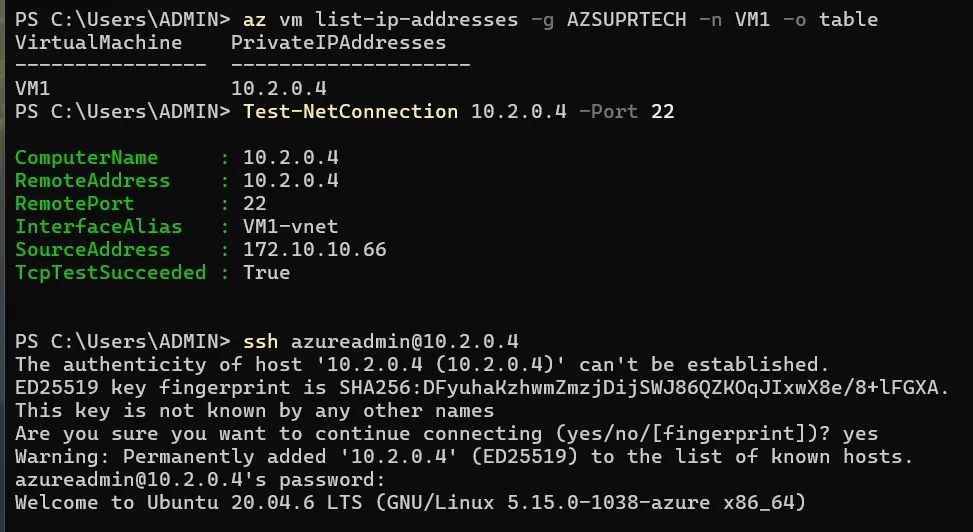
- Further our VM in the connected Subnet is also accessible directly over the VPN via SSH along with any other services we may want to access: